Appearance
Secrets
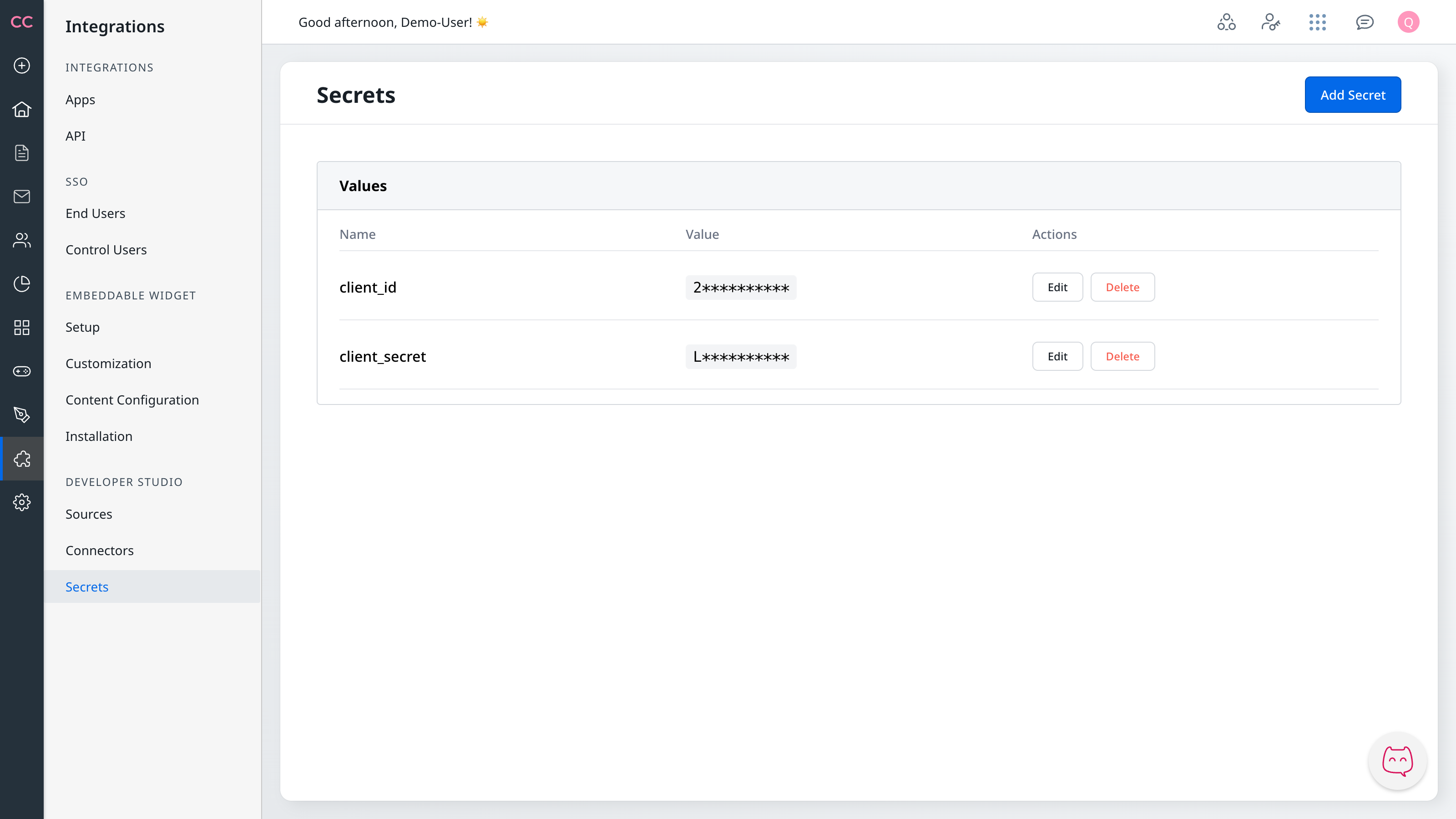
Secrets are encrypted key-value pairs that store sensitive information — API keys, OAuth credentials, tokens, and passwords — for use in connector configurations.
Navigate to Integrations → Developer Studio → Secrets to create, edit, and delete secrets.
Referencing secrets in connectors
Use the get_secret() function in a template expression to reference a stored secret:
jinja2
{{ get_secret('secret_name') }}The expression is replaced with the actual secret value when the connector executes. The value is resolved on the server and never exposed to the browser.
Where get_secret() is available
| Field | Available |
|---|---|
| Headers | Yes |
| Query Parameters | Yes |
| Authentication fields | Yes |
| URL templates | No |
| Payload templates | No |
| Response templates | No |
URL templates are rendered without access to secrets. Payload and response templates intentionally exclude secrets to prevent sensitive values from appearing in forwarded request or response bodies.
Naming rules
Secret names must be valid identifiers — letters, numbers, and underscores only. Names are case-sensitive.
Valid names:
api_keyoauth_client_idsalesforce_client_secretwebhook_secret_key
Invalid names (rejected on save):
api-key(contains hyphen)api key(contains space)123key(starts with number)api@key(contains special character)
Use descriptive names that include the service and purpose: salesforce_client_id, weather_api_key, stripe_webhook_secret.
Error handling
Secret not found
If you reference a secret that does not exist — or misspell its name — get_secret() preserves the original template expression literally in the rendered output. That literal string is sent to the external API, causing it to reject the request (typically 401 Unauthorized or 403 Forbidden).
How to diagnose:
- Use Test Connection — run a test in the connector editor and inspect the
X-Debug-Requestresponse header. If a field contains the rawget_secret('...')text instead of a resolved value, the secret name did not resolve. See Testing & Debugging. - Verify the name — open Integrations → Developer Studio → Secrets and confirm the secret exists with exactly the name you used. Names are case-sensitive.
- Check for typos — compare the name in
get_secret('name')with the Name column character-by-character.
Validation errors
| Error | Cause |
|---|---|
| Invalid secret name | Name contains hyphens, spaces, or special characters. See Naming rules. |
| Empty secret value | Secret values cannot be empty. |
| Duplicate secret name | A secret with this name already exists. Edit the existing secret or choose a different name. |
Troubleshooting
Secret value seems wrong — The masked display only shows the first character. Edit the secret and re-enter the value to confirm it is correct.
Credentials stopped working — Some API keys and tokens expire. Edit the secret to update with fresh credentials, then re-test the connector.
Template formatting — Use single quotes: get_secret('name'), not get_secret("name"). Avoid extra spaces: get_secret('api_key'), not get_secret( 'api_key' ).
Next Steps
- Authentication — Use secrets in API Key, OAuth, and JWT authentication
- Template Variables — Full reference of variables and functions
- Testing & Debugging — Verify secrets resolve correctly

